Cybercrime is more common than ever and is developing to be the most common type of crime that businesses face. Gone the days of physical theft and break in’s, now it is all virtual. Sadly, the opportunities are everywhere for these cyber criminals, with them logging in from unknow locations causing havoc, and with little to no penalties at all! It really is the perfect crime! Threats can be anything from skilled attacks, to ransomware, viruses, or social engineering to name a few.
Looking for ways to strengthen your business’s defence against cybercrime?
Our curated list of tips can help address common issues faced by other businesses. Don’t wait until it’s too late to act – start implementing these measures now to minimise the potential impact of cyber threats. Here are our 10 steps…
1. Conduct a Cybersecurity Assessment
Where do I start? The list could be endless. Fear not as lots of security providers can do the heavy lifting to help create a starting point by assessing your current security business posture, including Codestone. Our assessment can highlight areas of strength and improvement. It can also offer you recommendations for next steps, so it will save your internal team the work.
Contact Codestone to learn about the several Security Assessments available, including Microsoft (Office 365 and Azure) which is available on the Microsoft Market place, and our 66 points check. These traffic light-style reports show where improvements are needed and help you to plan the next steps ensuring your defence is a strong as possible. It also highlights what areas can be deferred if needed, due to budgets and resources.
2.Train your staff for any incident outcome
The adage ‘you are only as strong as your least knowledgeable member of staff’ is true when it comes to cybersecurity. Attackers can see weaknesses and where the easiest point of entry may be in your organisation; e.g., weak password like 123456, or that one person who opens a mistaken email.
One way to try and end this, is to have policies aligned to best practices against cybercrime and regularly remind and train your employees of these best practices policies. By embedding a regular training and reinforcement programme, you gain an added security layer to the cybersecurity protocols and support providers you engage. Contact Codestone today to learn about our security training and best practices services.
3. Ensure the latest software updates and roadmap for End-of-Life (EOL) technology
Software updates are often automatic and do not require monitoring, but there can be issues if updates are not automatic or if the product is approaching its End of Life (EOL). When a product reaches its EOL, it means that it will no longer receive any updates, technical support, bug fixes, or security patches. This can leave your system vulnerable to attacks and compromise your defence.
To ensure that your system is up to date and free of missing patches, it is recommended that you conduct routine manual checks for software updates. This will help to avoid potential security risks and keep your system running smoothly.
Contact Codestone today to learn more about CloudCare – our 24x7x365 IT support services to ensure you systems are up-to-date and that you have the right roadmap and support for EoL systems.
4. Install 24x7x365 defence monitoring
It’s important to remember that attacks can happen at any time, even outside of regular working hours. While your IT team may work from 8am-6pm, it’s crucial to consider who is checking your system during off-hours in case the worst happens. That’s where Security Incident & Event Monitoring (SIEM) software comes in, like Codestone’s partner solution from Bulletproof. By using SIEM, you can be alerted to any suspicious activity and prevent potential threats.
Consider using a Security Operations Center (SOC) service to watch your business 24/7. SOC services have added security experts who can supply round-the-clock monitoring and support. They have the ability and resources to act quickly and accurately in case of an attack, so you can rest easy knowing your business is in safe hands.
Don’t leave your system vulnerable – act now to protect your business around the clock. Contact Codestone today to learn more about our SIEM/SOC 24x7x365 services.
5.Put in place your Incident response plan
Plan, plan, plan… it is vital although it can sometimes feel overwhelming, but if you have a plan, it can pave the way for a quick and successful outcome from any cyber-attack or breach.
An Incident Response Plan is a pre-defined set of procedures to follow in response to a cybersecurity incident. This would include escalations paths, ensuring the right people are notified, and the right steps are taken and who owns which roles, amongst other measures and steps. There are other factors such as communication aspects, for both internal and external stakeholders too.
Codestone as the UK Top 50 Managed Service Providers can help you to scope this out. So let the expert consultants who have vast experience and knowledge, plan out the best course of action for your company.
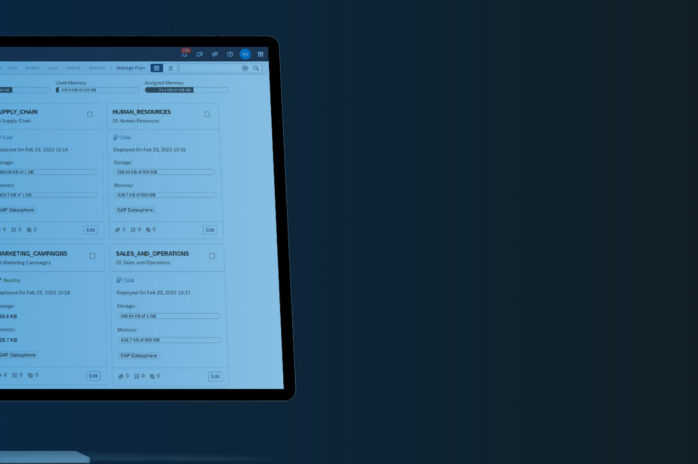
6. Set up privilege access management
With hybrid working, we are utilising so many more online tools, which store vital data. It is important to remember, staff tools, must be set up correctly and access privileges must be considered carefully. Not every member of your team needs administrative access, so consider the role, seniority, and other aspects, before applying a blanket approach to access. By doing this it minimises the issues and amount of damage that can happen if any attacker reaches someone with standard privileges.
Contact Codestone today to learn about SaaSLocker that can centrally and automatically ensure privileged access management across all your SaaS (Software as a Service) systems in one control area.
7. Throw up some physical barriers
With a strong awareness on digital threats, we mustn’t forget about the physical environment too. Sometimes, that is just how the threats begin, with attackers being onsite gaining access to login credential, infrastructure plans and other valuable information. So best practice needs to be always applied, from badge door entry to camera surveillance and proactive supervision of visitors. In addition, with hybrid working, employees need to be reminded of keeping discussions (while out) as private as possible.
8. Exterior cyber intelligence – be aware
Cyber assessment and reports are a great tool for insights and recommendations and vital for any organisation. It needs constant monitoring internally. You must also consider the external elements that cause influence on your business environment.
Further afield, dark web monitoring and cyber intelligence strategies could give you insight in planning and to what attackers may do, and how likely they are to target you. It will also give you insight into what types of information is already being exchanged in these undercover markets, helping you to craft a more robust strategy.
9. Assess vendors you work with and the risk
We have all heard the stories of how organisations become vulnerable from smaller third-party stakeholders such as vendors. To prevent this, you can put practices in place such as ensuring your suppliers have a Cyber Essential accreditation, furthermore a Cyber Essentials Plus certification. Or at least asking the questions about their systems and defence.
These processes need to be core in your company, to ensure you are not opening your organisation up to any vulnerabilities or incidents. To find out Codestone’s cybersecurity protocols, click here
10. Beware of BYOD (Bring You Own Device), it comes with its own issues
Hybrid working has its cons too, although organisations save on overheads. Mobile devices from tablets to mobile phones are forever going missing or being stolen, and the possibility with a growing hybrid workforce has increased with people working from anywhere and everywhere. It just takes one person to leave their phone on a train.
But it is not an end all if you have remote data protection set up. In best cases, you can track devices; in the worst, remote access can allow you to shut down log in all together or you can use encryption such as Multi-Factor Authentication (MFA). MFA is the simplest, most effective way to make sure users really are who they say they are. It is vital that this is considered when creating a security plan.
Did you get all that?